by Mel Hickey | Dec 18, 2023 | Information Security, Uncategorized
Revolutionising Security Awareness Training for Modern Enterprises In the ever-evolving digital landscape, organisations encounter a rising tide of sophisticated social engineering attacks. In this crucial defence line, where employees play a pivotal role, it becomes...
by Mel Hickey | Dec 18, 2023 | Information Security, Uncategorized
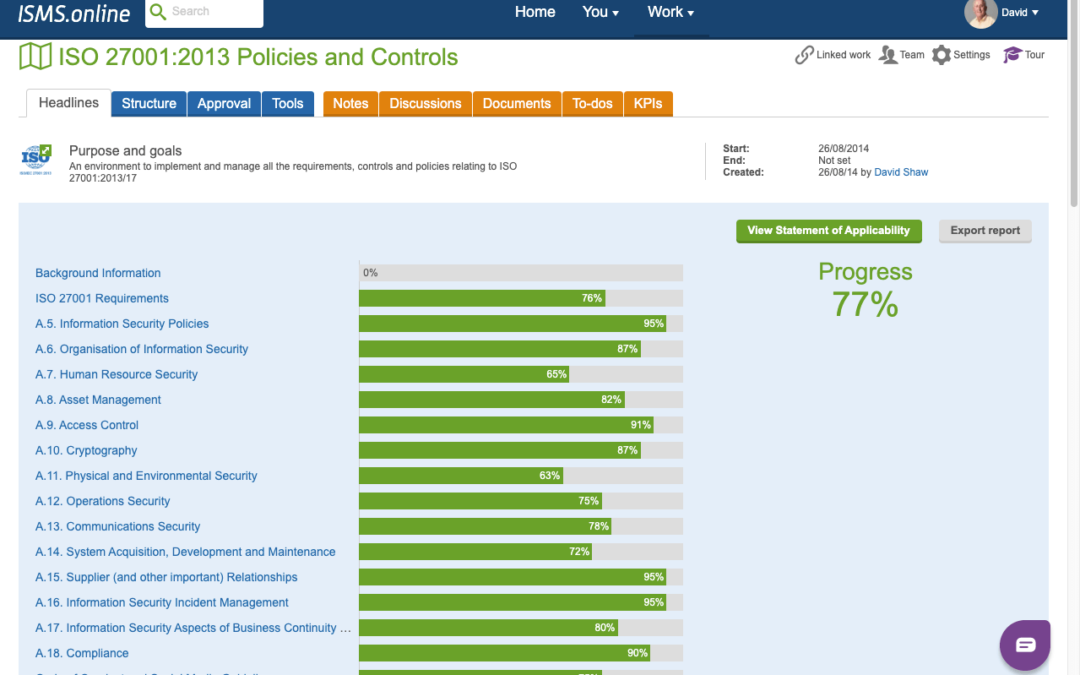
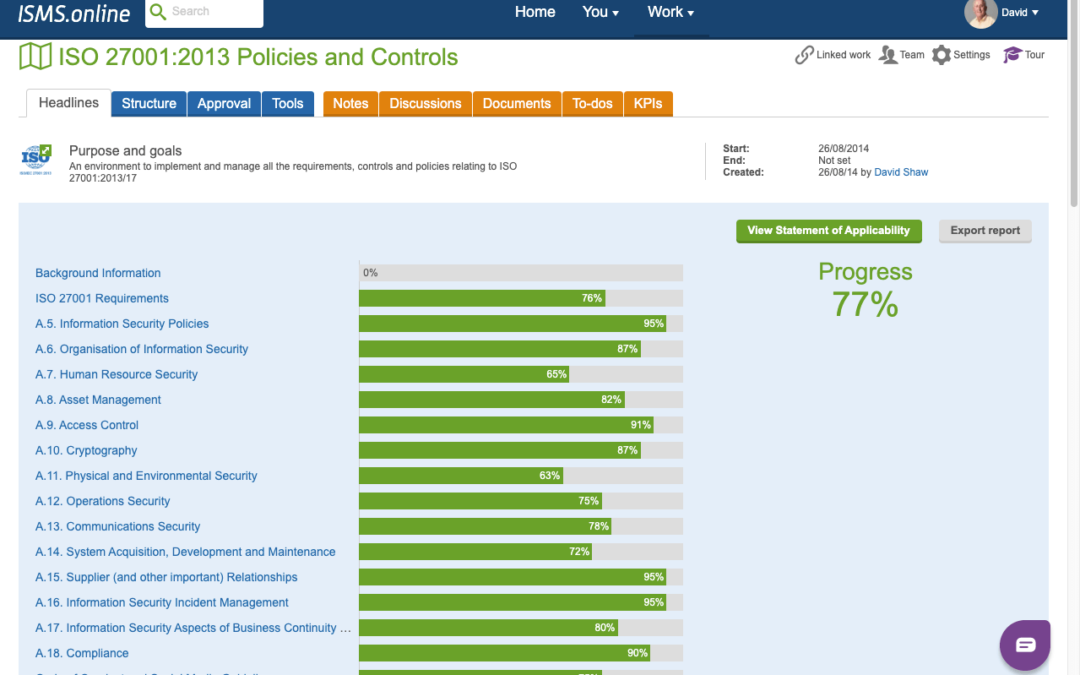
Unveiling the Efficiency of ISMS.online In the fast-evolving landscape of information security management, ISMS.online stands as a beacon, offering a cloud-based solution tailored for organisations striving to achieve and maintain ISO27001 certification. In...

by Mel Hickey | Dec 18, 2023 | Information Security, Uncategorized
Elevate your cybersecurity with SOC 2 Services In the ever-evolving cybersecurity landscape, businesses face mounting challenges in safeguarding their sensitive information. Resilient IT emerges as a stalwart ally, offering cutting-edge solutions to fortify your...

by Mel Hickey | Dec 18, 2023 | Information Security, Uncategorized
In the digital age, protecting personal and business information from malicious cyber threats becomes increasingly crucial. One of the most common and pernicious tactics used by cybercriminals is phishing. Understanding what constitutes a phishing attack and how to...
by Mel Hickey | Nov 14, 2023 | Information Security, Uncategorized
In the digital age, protecting personal and business information from malicious cyber threats becomes increasingly crucial. One of the most common and pernicious tactics used by cybercriminals is phishing. Understanding what constitutes a phishing attack and how to...

by Sjordan | Apr 8, 2022 | Uncategorized
With the increase of businesses moving to data-driven solutions comes the need for the implementation of information security best practises. Cue, ISO 27001. ISO 27001 is a globally recognised international standard focussed on information security management that...